Table of contents
Modern teams collaborate across departments, agencies, contractors, clients, and sometimes more. That keeps work moving, but it also creates more ways for sensitive content to spread too widely, get copied into the wrong tool—or fall out of sync.
The best secure collaboration tools help you work quickly without giving up control. If you’re evaluating options, start with this simple rule—a secure collaboration tool should protect content, limit access, show you what happened, and still feel easy enough that people want to use it.
Choose a Dropbox plan that fits your team, or explore the full range of collaboration features if you want to see exactly how it can match powerful capabilities to your security requirements.

What’s a secure collaboration tool?
A secure collaboration tool is a platform that lets people share, review, edit, collect, and deliver work while keeping the right controls around that content. It isn’t just a storage location—it’s the system a team uses to keep collaboration moving without losing visibility, permissions, or control.
A single tool generally should support daily collaboration, external sharing, file collection, review, and final delivery. When those steps happen across too many disconnected apps—the security risk goes up fast.
How secure is file collaboration in the cloud?
File collaboration in the cloud can be very secure, even for sensitive content, if the platform includes the right controls. Tools like Dropbox use encrypted storage and transfer, strong sign-in protection, clear permissions, and activity history—for the highest levels of security.
Cloud collaboration becomes risky when:
- Access is too broad
- Links never expire
- Outside collaborators are unmanaged
- Teams work around official tools because the approved one feels too hard to use
In other words, cloud collaboration itself isn’t the problem—poor controls and poor adoption are.
6 secure collaboration features you should look for
When assessing controls and features in collaboration tools for your team, consider the following:
1. Encryption that fits the sensitivity of your work
Start with encryption in transit and at rest. For highly sensitive projects, look for advanced options such as end-to-end encryption (E2EE) or customer-controlled key management. Encryption matters, but it’s only one part of the picture.
With encryption, you can:
- Encrypt sensitive project folders by default, so sharing doesn’t require extra steps—and your team can move fast without second-guessing security
- Reduce the blast radius of leaks and support trust, audit readiness, and regulated work—while avoiding slow delivery
2. Identity and access controls
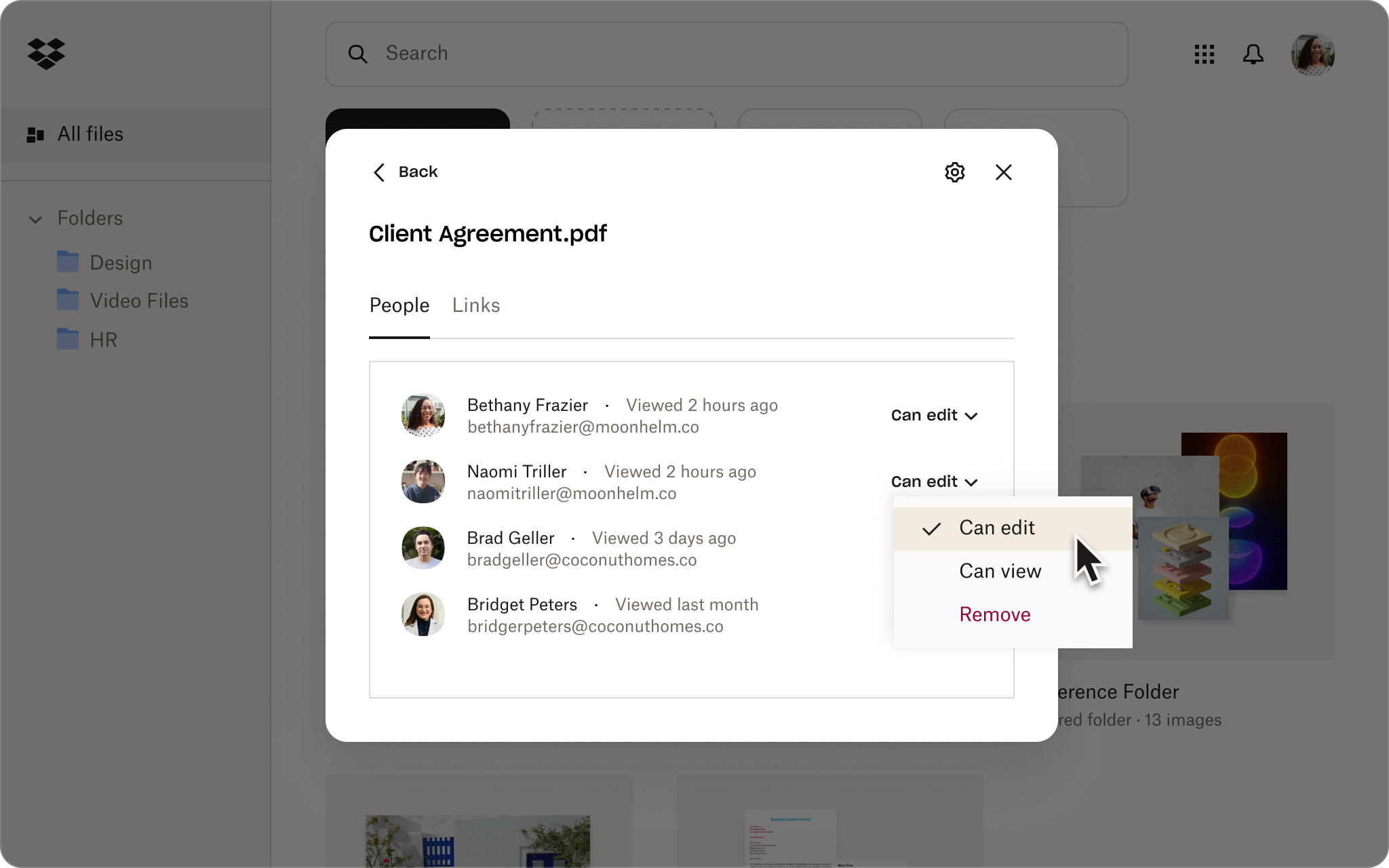
A secure platform should support role-based access, least-privilege file permissions, and strong sign-in options such as multi-factor authentication or single sign-on. You should be able to decide who can view, edit, comment, download, or reshare content.
With access controls, you can:
- Assign roles at the folder level and use multi-factor authentication—so your team spends less time fixing access issues and more doing work
- Reduce account compromise risk and make it easier to enforce consistent policies across teams—including partners or external contractors
3. Secure external sharing controls
This is where many tools fall short. You need file sharing with view-only access, password protection, expiration dates, and download restrictions—with a simple way to unshare when a project ends or a relationship changes.
With secure sharing, you can:
- Share externally with view-only access and passwords or expiration dates—so your team can collaborate with partners and avoid losing control after you hit send
- Lower the risk of accidental oversharing with external controls, which help protect IP, client data, and your company reputation
4. Admin visibility and reporting
Good security shouldn’t feel invisible when you need answers. Look for activity logs, sharing reports, alerts, and a central admin view. If something is shared outside the team, you should be able to see it and respond quickly.
With admin-level security controls, you can:
- Use activity logs and alerts to catch unexpected sharing early—so your team can resolve issues before the damage is done
- Strengthen incident response and governance, helping you prove due diligence and reduce the cost of investigations
5. Governance, compliance, and recovery
Enterprise teams may need data classification, data loss prevention alerts, retention policies, legal hold support, and integrations with existing security systems. Teams of any size should also look for version history and file recovery, because mistakes and overwrites are part of real collaboration.
With data governance, you can:
- Apply retention and version history to key project folders—so your team can undo mistakes quickly instead of rebuilding lost work.
- Reduce legal and compliance risks while preventing costly downtime when files are deleted, overwritten, or disputed
6. Integrations and ease of adoption
The most secure tool isn’t the one with the longest feature list. It’s the one your team will use. Look for a platform with a wide range of app integrations that fits into existing workflows and works well with the tools your team already depends on.
With adoption-driving app integrations, you can:
- Connect the tools your team already uses so sharing happens in the flow of work—for less copy-and-paste moments, fewer side channels, and more consistency
- Reduce use of shadow tools and create a stronger security posture overall, because policies get followed in real life
How to manage secure collaboration across external teams
External collaboration is where things get real—agencies, freelancers, clients, vendors, and so on. The goal isn’t to lock everything down—it’s to give the right people the right access for the right amount of time, without losing visibility or control.
One key distinction—encryption protects the content (at rest and in transit). Secure file sharing adds the controls around it—who can access it, what they can do, how long access lasts, and whether activity is logged. Encryption is essential, but it’s only part of the setup.
Here’s what a practical external-collaboration approach might look like:
- Ongoing work—shared folders with clear roles, comments, and version history
- Review-only—view-only links with passwords, expirations, and download restrictions
- Collecting files—file requests, so partners can upload without seeing your internal folders
- Final delivery—file transfer links that send a copy, not your live workspace
For larger operations, you’ll also want the basics that make governance stick—like multi-factor authentication, role-based access, device controls, audit logs, and compliance support—but it all has to be easy enough that people don’t fall back to using attachments or personal drives.
The best secure collaboration tools make these guardrails feel effortless, so your team can work with external partners in the same flow—minus the stress.
Why Dropbox is a strong choice for secure collaboration
Secure collaboration is like hosting a party for your files. You want easy access, the right people in the right places, and control over when it ends.
Dropbox makes this simple while keeping things secure. Here’s what that looks like in practice:
- Share links with guardrails, not vibes: Passwords, expiration dates, and download restrictions turn a shared link into a controlled guest pass—not an open invitation.
- Keep admins in the driver’s seat: External sharing settings, approved people and domains, activity monitoring, and admin-console reporting mean you get a dashboard with receipts.
- Turn sensitive workflows into locked-room workflows: For higher-security needs, Dropbox supports advanced key management and end-to-end encryption. Think of it as moving from a good lock to a vault you can audit.
- Spot risk before it turns into regret: Data classification and alerts help flag sensitive content early—highlighting “maybe don’t overshare this” moments.
- Reduce device risk when the real world happens: Device approvals and remote wipe help when laptops disappear, phones get lost, or a contractor’s device shouldn’t have access anymore. Essentially, an emergency shutoff switch keeps you in control.
- Give your team a safety net (because they’re humans): Version history and file recovery help undo overwrites, accidental edits, and occasions when someone uses the wrong file. That way, one mistake doesn’t become a full-on archaeological dig.
- Support different collaboration styles without forcing one workflow: Shared folders for active work, file requests to collect content safely, and Dropbox Transfer for polished one-way delivery—so you can switch modes depending on your needs.
The best part is the flexibility. Dropbox works whether you’re collaborating inside one team or with departments, agencies, clients, and vendors—without turning every share into a security project.
Make secure collaboration easier with Dropbox
Secure collaboration tools help fast-moving teams protect sensitive content. When you have the right mix of visibility and flexible sharing controls—it becomes easier to collaborate confidently.
Dropbox brings those capabilities together in one place, so your team can share, review, collect, and deliver content more securely. Choose a plan to find the right fit for your team.
Frequently asked questions
Cloud file storage can be secure for sensitive data when it includes strong encryption, access controls, admin visibility, and clear sharing policies. Sensitive content shouldn’t live in tools where links stay open indefinitely or where outside access is hard to track and revoke.
There’s no single best platform for every team. The best platform for file collaboration depends on how you work, who you share with, and how much control your admins need. If you want secure sharing, external collaboration, version control, and strong admin visibility in one place, Dropbox is a strong option.
Yes. The best secure collaboration tools let you choose the right level of access for each situation. In practice, that could mean file permissions, a view-only link for review, a file request for inbound documents, a shared folder for active project work, or a transfer for final delivery.
Yes. Smaller teams often work with outside partners and move quickly, which makes secure defaults even more important. Simple controls like passwords, expiration dates, version history, and easy admin visibility can prevent the kinds of mistakes that create delays, confusion, or unnecessary risk.


