Что происходит за кулисами: обзор архитектуры
В Dropbox разработано несколько уровней защиты: в частности, мы используем безопасную передачу данных, шифрование, конфигурацию сети, а также элементы управления на уровне приложений, распределенные по масштабируемой, безопасной инфраструктуре.
Файловая инфраструктура
Пользователи Dropbox в любой момент могут получить доступ к своим файлам и папкам через разные интерфейсы (например, программу Dropbox, Интернет и мобильные приложения, а также через сторонние программы и приложения, связанные с Dropbox). В каждом из них имеются функции и настройки безопасности, которые защищают и обрабатывают данные пользователя, обеспечивая при этом удобный доступ. Все наши программы и приложения используют защищенные серверы для предоставления доступа к файлам, позволяя делиться ими с другими пользователями и синхронизировать подсоединенные устройства, когда пользователь добавляет, изменяет или удаляет файлы.
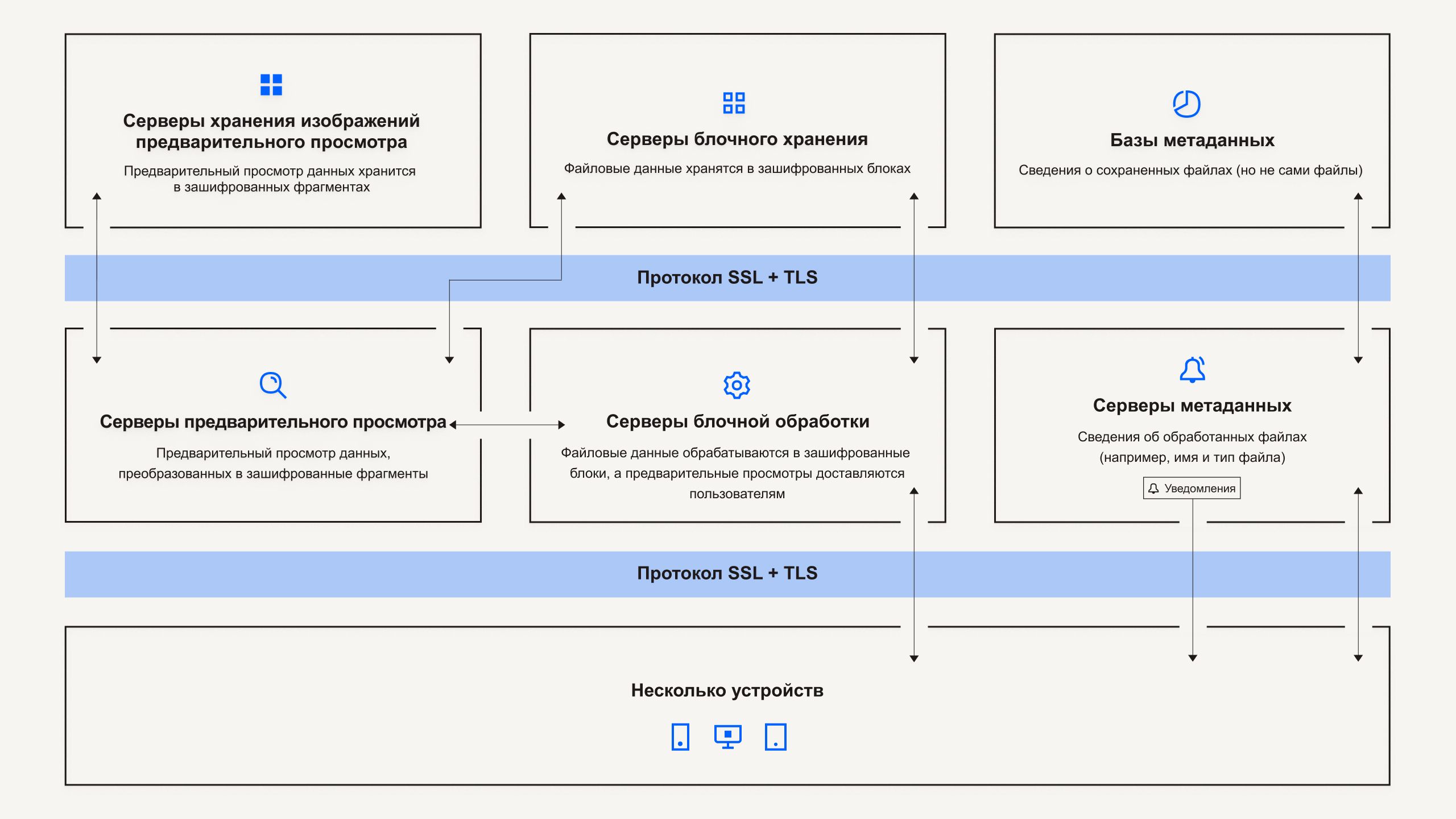
Наша файловая инфраструктура состоит из следующих компонентов:
Серверы метаданных
Некоторая основная информация о данных пользователей называется метаданными, которые хранятся в отдельном хранилище и являются своего рода каталогом данных в аккаунтах пользователей. Метаданные включают в себя базовые сведения об аккаунте и пользователе, например адрес электронной почты, имя и названия устройств. Метаданные также включают в себя базовые сведения о файлах, в том числе названия и типы файлов, которые помогают поддерживать такие функции, как журнал версий, восстановление и синхронизация.
Базы данных метаданных
Метаданные файлов хранятся в службе базы данных на основе MySQL, и их разделение и репликация осуществляются по мере необходимости с целью обеспечения соответствия требованиям в отношении эффективности и высокой доступности.
Блокировка серверов
Благодаря своему дизайну Dropbox предоставляет уникальный механизм безопасности, который выходит за рамки традиционного шифрования для защиты пользовательских данных. Серверы блочной обработки выполняют обработку файлов из приложений Dropbox: файлы делятся на блоки, каждый из которых кодируется с помощью криптостойкого шифра, при этом синхронизация применяется только к тем блокам, в которые были внесены изменения после создания очередной версии файла. При обнаружении приложением Dropbox нового файла или изменений в существующем файле такое приложение передает серверам блочной обработки уведомление об изменениях, после чего выполняется обработка новых или измененных файловых блоков с последующей передачей этих блоков на серверы блочного хранения. Серверы блочной обработки также используются для передачи файлов и изображений предварительного просмотра пользователям.
Серверы блочного хранения
Серверы блочного хранения позволяют хранить содержимое файлов пользователей в виде зашифрованных блоков. Серверы блочного хранения позволяют хранить содержимое файлов пользователей в виде зашифрованных блоков. Перед пересылкой программа Dropbox разбивает файлы на блоки файлов при подготовке к хранению. Серверы блочного хранения действуют как система хранения данных с адресацией по содержимому (Content-Addressable Storage — CAS), причем каждый индивидуальный зашифрованный блок файлов вызывается на основе его хеш-значения.
Серверы предварительного просмотра
Серверы предварительного просмотра отвечают за создание предпросмотра файлов. Предварительный просмотр — это рендеринг файла пользователя в другой формат, который больше подходит для быстрого отображения на устройстве конечного пользователя. Серверы предварительного просмотра вызывают блоки файлов с серверов блочного хранения для генерации изображения предварительного просмотра. При запросе предварительного просмотра файла серверы предварительного просмотра вызывают кэшированное изображение предварительного просмотра с серверов хранения изображений предварительного просмотра и передают его на серверы блочной обработки. В конечном итоге предварительный просмотр для пользователей обеспечивают серверы блочной обработки.
Серверы хранения предварительных просмотров
Кэшированные версии файлов для предварительного просмотра хранятся в зашифрованном виде на серверах хранения предварительного просмотра.
Служба уведомлений
Это отдельная служба для отслеживания изменений в данных аккаунтов Dropbox. Данная услуга не пересылает никаких данных или метаданных. Каждая программа Dropbox подключается к службе уведомлений методом длинных опросов и переходит в режим ожидания. Когда происходит изменение какого-либо файла в Dropbox, служба уведомлений сообщает об изменении соответствующей(-им) клиенту(-ам), закрывая соединение методом длинных опросов. Закрытие соединения сигнализирует о том, что программа Dropbox должна безопасно подключиться к серверам метаданных для синхронизации любых изменений.
Инфраструктура Dropbox Paper
Пользователи Dropbox могут войти в документы Paper когда угодно через сайт и мобильные приложения или сторонние приложения, подсоединенные к приложению Dropbox Paper. Все наши программы и приложения используют защищенные серверы для предоставления доступа к документам Paper, позволяя делиться ими с другими пользователями и синхронизировать подсоединенные устройства, когда пользователь добавляет, изменяет или удаляет документы.
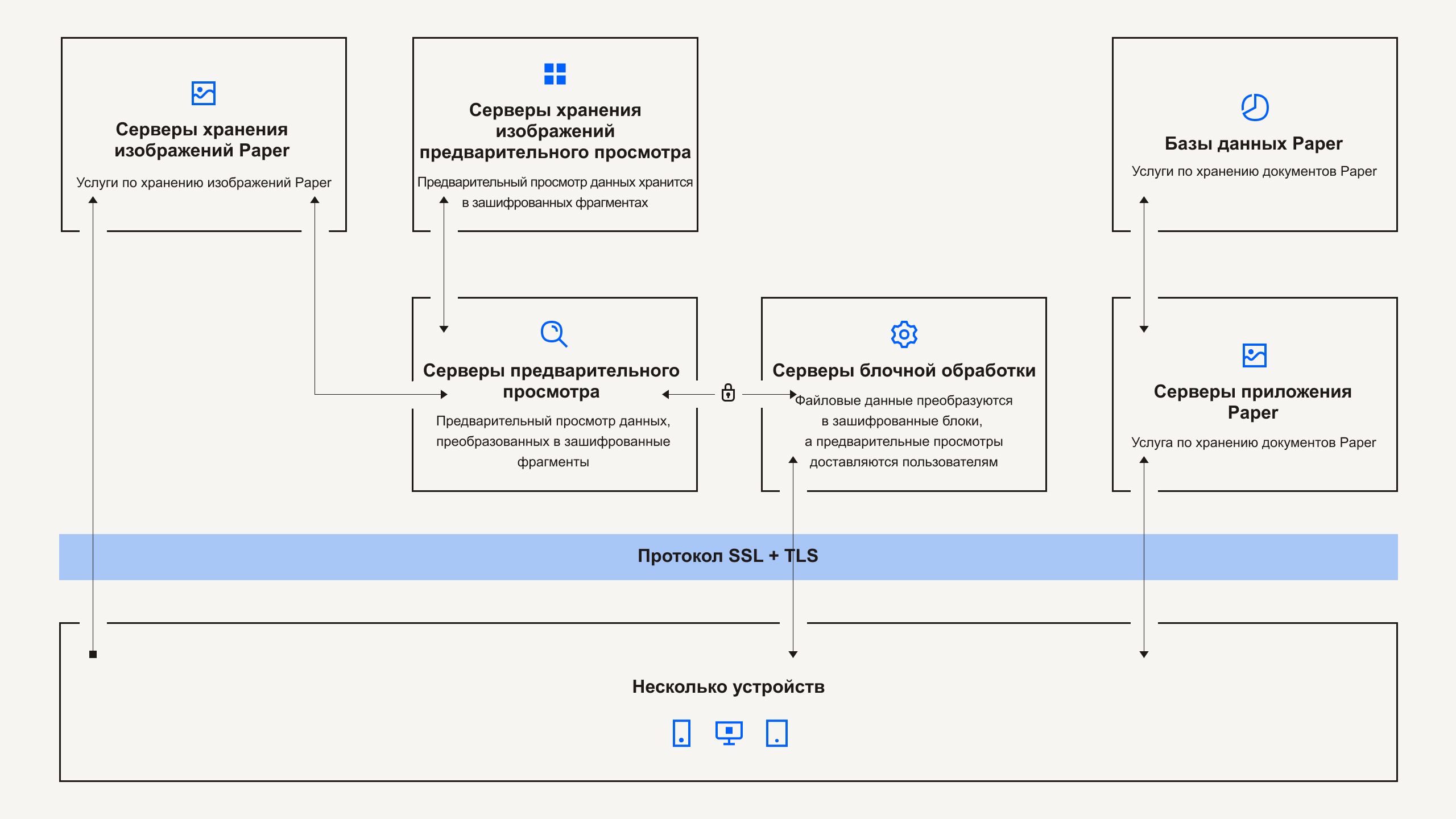
Инфраструктура Dropbox Paper состоит из следующих компонентов:
Серверы приложений Paper
Серверы приложения Paper обрабатывают запросы пользователей, передают документы Paper со внесенными изменениями обратно пользователям и осуществляют работу, связанную с уведомлениями. Серверы приложения Paper записывают внесенные пользователями изменения в базы данных Paper, где они помещаются на постоянное хранение. Сеансы связи между серверами приложения Paper и базами данных Paper шифруются с помощью криптостойкого шифра.
Базы данных Paper
Содержимое документов Paper, принадлежащих пользователям, а также определенные метаданные, относящиеся к этим документам, хранятся в зашифрованном виде в базах данных Paper. Сюда относится информация о документе Paper (например, его название, список участников, имеющих к нему доступ, права доступа, проекты или папки, с которыми связан этот документ, и другие данные), а также содержимое самого документа Paper, включая комментарии и задания. Разделение и репликация баз данных Paper осуществляются по мере необходимости с целью обеспечения соответствия требованиям в отношении эффективности и высокой доступности.
Серверы метаданных
Для обработки информации о документах Paper, такой как журнал изменений файлов Paper и список участников общей папки, служба Paper использует те же серверы метаданных, описание которых дано на схеме инфраструктуры Dropbox. Компания Dropbox напрямую управляет серверами метаданных, которые размещены в сторонних центрах хранения и обработки данных, использующих принцип совместного размещения.
Базы метаданных
Для хранения информации о документах Paper, такой как права доступа, разрешения и ссылки на папки, служба Paper использует те же базы метаданных, описание которых дано на схеме инфраструктуры Dropbox. Метаданные документов Paper хранятся в службе баз данных на платформе MySQL. При необходимости их можно сегментировать и реплицировать, чтобы обеспечить соответствие требованиям к быстродействию и высокой доступности.
Серверы хранения изображений Paper
Загружаемые в Paper изображения хранятся в зашифрованном виде на серверах изображений Paper. Передача изображений между приложением Paper и серверами хранения изображений Paper выполняется в рамках зашифрованного сеанса.
Серверы предварительного просмотра
Серверы предварительного просмотра создают изображения предпросмотра как для изображений, загруженных в документы Paper, так и для гиперссылок, встроенных в документы Paper. В случае изображений, загруженных в документы Paper, серверы предварительного просмотра получают данные изображений, хранящихся на серверах хранения изображений Paper, через зашифрованный канал. В случае гиперссылок, встроенных в документы Paper, серверы предварительного просмотра получают данные изображений и создают изображения предварительного просмотра с использованием шифрования, как указано в ссылке на источник. В конечном итоге изображения предварительного просмотра передаются пользователям серверами блочной обработки.
Серверы хранения изображений предварительного просмотра
Серверы хранения изображений предварительного просмотра. Для хранения изображений предварительного просмотра в Paper используются серверы хранения изображений предварительного просмотра, указанные на диаграмме инфраструктуры Dropbox. Блоки кэшированных изображений предварительного просмотра хранятся в зашифрованном формате на серверах хранения изображений предварительного просмотра.
Защиту этих служб обеспечивают как специальные внутренние службы безопасности, так и сторонние специалисты: они выявляют и устраняют риски и уязвимости. Эти группы регулярно проводят тестирование и аудит приложений, сети и других объектов, чтобы обеспечить безопасность внутренней сети. Кроме того, наша политика ответственного разглашения предписывает поиск уязвимостей в системе безопасности и сообщение о них.
Центры обработки данных
Корпоративные и производственные системы Dropbox располагаются на мощностях сторонних центров обработки данных и поставщиков управляемых услуг, которые находятся в США. Эти сторонние поставщики услуг отвечают за управление физической, экологической и операционной безопасностью на границах инфраструктуры Dropbox. Dropbox отвечает за логическую, сетевую и связанную с приложениями безопасность нашей инфраструктуры, расположенной в сторонних центрах обработки данных.
Шифрование
Хранящиеся неактивные файлы Dropbox и документы Dropbox Paper шифруются с помощью 256-битового стандарта Advanced Encryption Standard (AES). Чтобы защитить данные при передаче между приложениями Dropbox (в настоящее время это программа для компьютера, мобильное приложение, API и сайт) и нашими серверами, Dropbox использует протокол SSL/TLS для передачи данных, создавая безопасный туннель, защищенный не менее чем 128-битовым шифрованием стандарта AES. Точно таким же образом данные при передаче между приложениями Paper (мобильное приложение, API и сайт) и размещенными службами шифруются по протоколу SSL/TLS.
Привязка сертификата
Dropbox использует технологию привязки сертификата в своих программах для компьютера и мобильных приложениях, предназначенных для синхронизации файлов и общего доступа. Привязка сертификата — это дополнительная проверка, гарантирующая, что наши клиенты будут подключаться только к серверам с цифровыми сертификатами из утвержденного списка центров сертификации. Мы используем эту проверку для защиты от злоумышленников государственного уровня, контролирующих мошеннические центры сертификации, а также для защиты от локальных вредоносных программ, которые могут перехватывать ваши соединения.
Совершенная прямая секретность
Для контролируемых нами конечных точек (программ для компьютеров и мобильных приложений) и современных браузеров мы используем надежное шифрование и поддерживаем совершенную прямую секретность. Свойство совершенной прямой секретности не позволяет использовать наш закрытый ключ сертификата для расшифровки интернет-трафика. Это добавляет дополнительный уровень защиты для зашифрованных соединений с Dropbox, надежно отделяя каждый сеанс ото всех предыдущих. Кроме того, в браузерах мы включаем атрибут Secure для всех файлов cookie, используемых для проверки подлинности, а также используем HSTS (политику строгой безопасности передачи информации по протоколу HTTP).
Управление ключами
Инфраструктура управления ключами Dropbox включает в себя операционные, технические и процедурные меры обеспечения безопасности, предусматривающие ограничение прямого доступа к ключам. Создание, обмен и хранение ключей шифрования — распределенный и децентрализованный процесс.
Dropbox шифрует файлы от лица пользователя, чтобы понизить сложность, внедрить расширенные функции и включить мощный криптографический контроль. Создание, хранение и защита ключей шифрования файлов обеспечиваются средствами управления защитой рабочей инфраструктуры и политиками безопасности. Доступ к рабочим системам ограничен уникальными парами ключей SSH. Политики и процедуры безопасности предусматривают обязательную защиту ключей SSH. Внутренняя система управляет процессом безопасного обмена открытыми ключами, а закрытые ключи хранятся в безопасности.
Подробную информацию о наших функциях, связанных с контролем и прозрачностью, можно найти в Центре управления безопасностью.